Project Epsilon
SCP: Sovereignty & Control Protocol
AI Safety
AI Safety is an issue that I took very seriously as I delved into AI-work and self taught myself using various LLMs and AI models, from learning the architecture of models and running locally hosted open source models, to generating and collaborating with others on the internet.
The idea that AI can operate without continuous human authorization, grow independent of humanity, and be malicious in nature, is a real problem that many frontier labs seek to tackle. Over 60+ iterations, and presumably with more to come, I have attempted to tackle this problem through extensive research and reverse engineering. Named after the character Maki Zenin from popular shonen Jujutsu Kaisen, I have come up with a hardware-backed constraint, the Maki constraint, that serves as the foundation of my research paper, the Sovereign Compute Protocol.
Maki Zenin is cursed with a Heavenly Restriction, sacrificing all cursed energy (in a world where cursed energy is the premier currency of power) for unparalleled levels of physical endurance, strength, and prowess. Similarly, my Maki constraint is embedded not in software policy or model alignment, but at the hardware layer where it cannot be abstracted away, patched around, or quietly overridden. Every inference cycle requires an active, cryptographically-verified human authorization signal before execution proceeds.
In summary, think of this proposition as a virtual sandbox in which hardware-level verification is needed for autonomous AI to be safely monitored and developed beyond current limitations.
// TECHNICAL ARCHITECTURE
Hardware Security Modules
HSM · CRYPTOGRAPHIC ENFORCEMENTDedicated cryptographic hardware that manages key generation, storage, and signing operations in a tamper-resistant environment. In SCP, HSMs act as the root of trust, enforcing authorization policies at the silicon level before any AI computation begins. Keys never leave the module; all enforcement is hardware-native.
Trusted Execution Environments
TEE · ISOLATED EXECUTIONTEEs create isolated secure enclaves within processors, partitioned from the main OS, hypervisor, and any other running software. SCP routes all AI model inference through TEE-isolated execution contexts. Even if the surrounding system is compromised, the AI's execution environment remains sealed and auditable.
Distributed Oversight
OVERSIGHT · MULTI-PARTY CONTROLNo single human or institution holds unilateral control. SCP distributes authorization across a consensus network of independent oversight nodes. High-stakes AI operations require threshold signatures from multiple parties, preventing capture, corruption, or single-point failure from subverting the protocol.
Human Sovereignty Layer
SOVEREIGNTY · CONTINUOUS AUTHSCP establishes human sovereignty at the hardware layer, the only layer that cannot be abstracted away. Software alignment can be fine-tuned away. Constitutional AI can be argued around. Hardware cannot. By anchoring control at silicon, SCP ensures that human intent remains the irreducible prerequisite for all AI operation.
Attestation Chain
ATTESTATION · VERIFIABLE PROOFEvery SCP-compliant execution produces a cryptographic attestation: a verifiable proof that the model ran inside an authorized TEE with valid HSM-backed credentials. Attestation chains are tamper-evident logs that enable post-hoc auditing of any AI decision or action taken under the protocol.
Kill Switch Architecture
TERMINATION · HARD HALTSCP integrates hardware-level termination authority: not a software flag, but a physical interrupt pathway that can be triggered by authorized parties to halt AI execution instantly. The kill switch is cryptographically gated and distributed, preventing both accidental activation and adversarial blocking.
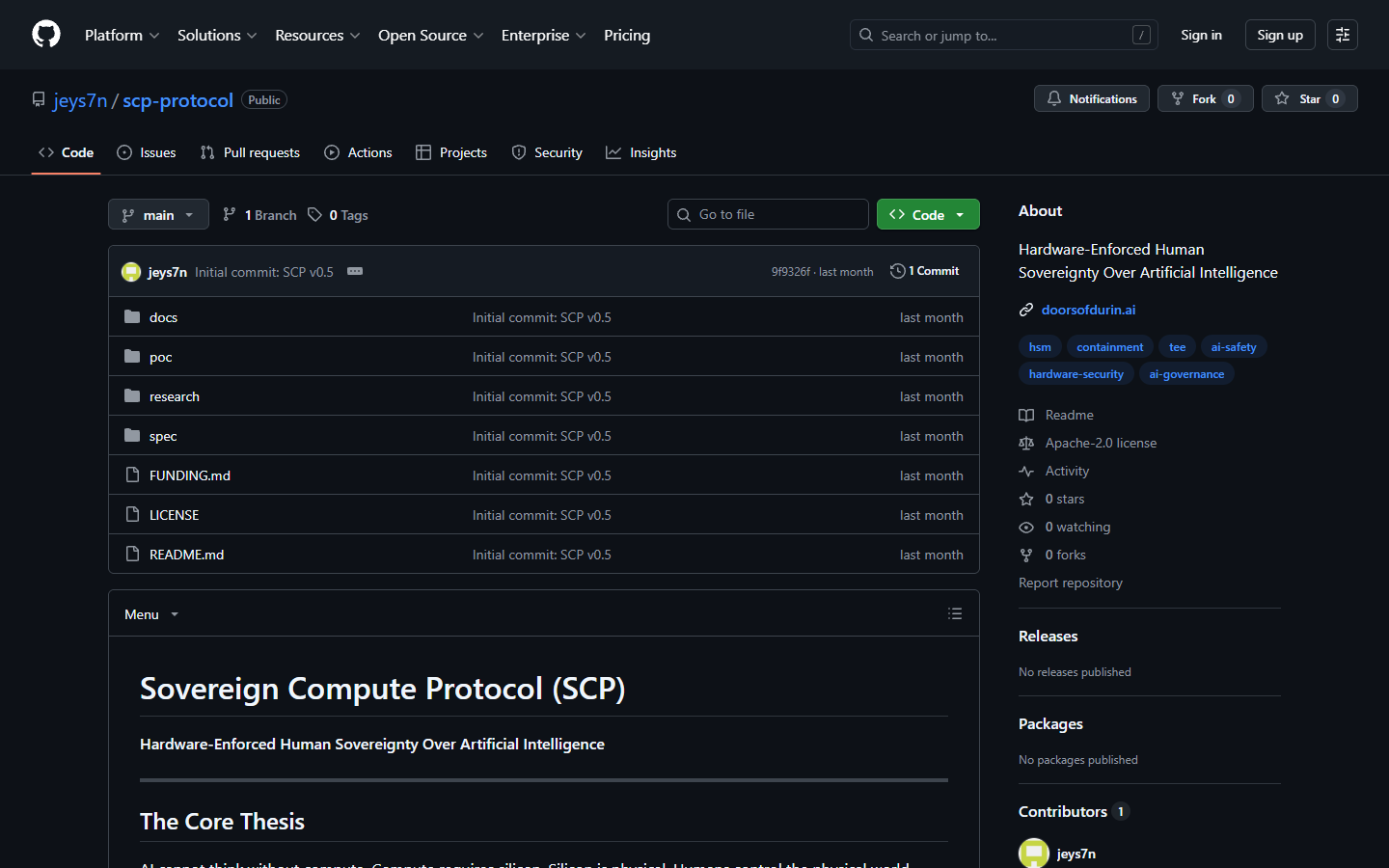
SCP Protocol
github.com/jeys7n/scp-protocol ↗The SCP Protocol repository contains the full specification, architecture documentation, and reference implementation for establishing human sovereignty over AI at the hardware layer. Includes HSM integration specs, TEE configuration guides, distributed oversight consensus design, and the Maki constraint formal definition.